Introduction
cloud-based email services are a growing industry standard as a lot of companies prefer to transfer the risk of storing and transmitting data to trust 3rd parties rather than maintain their own systems. These cloud-based email applications depend on centralised and trusted authentication methods to keep email data safe.
With the rise of threat actors in recent years, companies such as Microsoft have become target to sophisticated attacks from threat actors like the Chinese state-affiliated threat actor Storm-0558. In 2023, Storm-0558 targeted the Microsoft authentication system that handles email login.
In summary, the attackers, Storm-0558, forged authentication tokens used to authenticate with Microsoft cloud email accounts to access emails from government agencies. This was done by forging the token and using the token to impersonate legitimate users trying to access their email accounts.
A lot of high-level US government agencies were surgically targeted, including, but not limited to, high-value diplomatic email accounts.
The Identity trust system was supposed to be cryptographically secure and impenetrable and was trusted by a lot of high-level government agencies and companies worldwide.
The hack that took place raised serious questions about cloud identity trust models and how secure they are, as well as the weaknesses they possess. The attack also proves that cloud risk transfer does not eliminate the risk but redistributes the very real threat that can still affect the end client.
This blog will explain the attack vector, the vulnerability that Storm-0558 exploited, mitigation strategies and the reputation loss for both the client and host company, Microsoft.
Attack Vector
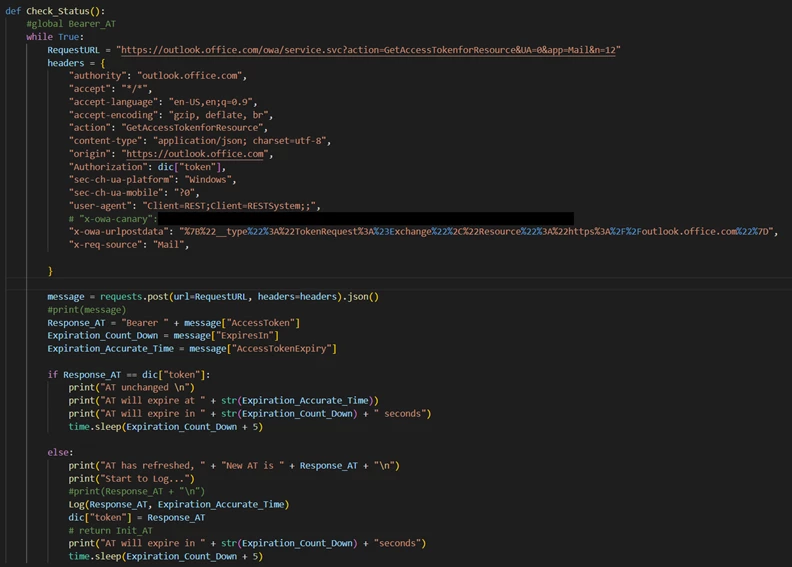
The first step the Chinese state-affiliated espionage group Storm-0558 used to access the emails was to obtain access to a Microsoft engineer’s account/computer to gain access to a testing/debug environment that contained raw data from secure systems the engineer would have used to look for bugs. Compared to the live environment, the debug environment is a lot less locked down and shows logic that would otherwise be difficult to access. Accessing the engineer's computer/account with the debug would be considered a side door approach. Instead of going straight after government emails, they hacked into and gained access to a computer used by 3rd-party contractors who work with the government.
Even with the debug environment alone, Storm-0558 would be unable to attack the main environment. The next big breakthrough Storm-0558 had was a crash dump. A crash dump is a file/snapshot that contains all the processes and memory at the time the system crashes. In April 2021, the Microsoft consumer signing system crashed, and because of a race condition bug, it leaked a highly sensitive cryptographic key. This key was the 2016 Microsoft services account consumer signing key. The crash dump was ultimately found in the debug environment of the Microsoft engineer who was compromised, leading Storm-0558 to get their hands on the secret cryptographic key.
When the crash dump was created, it was moved to a lower security debug environment for engineers to analyse. This one move was a critical security flaw as it went from a high zone to a low security zone without human intervention. The internal scanning tools that should have detected the cryptographic key being present in the crash dump failed to detect it. This scanner has the purpose of deleting passwords and secret keys before giving them to the debug team, as they should not be seen by humans. The fact that Storm-0558 were in a Microsoft account that was in a debug environment, which had authorisation to be inside of, and the scanning failed; when Storm-0558 extracted the key from the crash dump, it did not raise any alarms.
The stolen key from the crash dump on the debug environment allowed Storm-0558 to forge their own IDs and use the key to sign them. These IDs allowed Storm-0558 to bypass security measures like passwords and MFA to give silent, unlimited access to government emails.
Vulnerability Exploited
There are two types for key that Microsoft use for everyday use. The Microsoft consumer and Microsoft enterprise key.
The Microsoft consumer key is specifically made for signing in Microsoft accounts for everyday people using services like Xbox Live or a free Outlook.com email address, allowing the end user to access their account.
Microsoft Entra ID (Previously named Azure Active Directory) is a completely different system from Microsoft consumer Key sign-on; it is a highly secure identity system made for enterprise clients, specifically with enterprise customers in mind. These customers include large companies and government agencies from around the world.
The two ID systems mentioned previously should never interact with each other, as they have fundamentally different infrastructures and use cryptographic keys to secure different systems. This means the one cryptographic key should not mathematically be able to be used to unlock the other system.
Storm-0558 took the tokens they forged using the consumer MSA key and injected them into Microsoft’s Enterprise systems, specifically the enterprise business Outlook.com email service. When Storm Storm-0558 gave the enterprise Outlook.com API the token that was generated with the stolen key, the API performed a normal cryptographic check to verify that the token was signed using a valid key.
The underlying math of the signature algorithm worked perfectly and recognised the token as authentically signed; this ultimately allowed Storm-0558 to access the accounts on the enterprise Outlook.com service.
When the system checked for authenticity, it failed to check if the key can be used for enterprise authentication rather than just the consumer authentication system. This resulted in an invalid hierarchy of ownership and authentication; this allows anyone with a signed token using the enterprise key to sign into the enterprise Outlook.com accounts.
Besides the keys having a bad hierarchy, the consumer key stolen should not have been active in the first place. This brings up the issue of keys not expiring; the key was from 2016 and worked in 2023. This vulnerability is sometimes considered a zombie key, as the key should be deactivated (dead) but is still working (alive). Normally, a system like MSA would have key rotations and better security implications to stop this issue.
Microsoft’s internal logging was inadequate and was blind to the attack Storm-0558 was conducting. The logs that the US Government used to detect it in the end were from a paywalled feature that only companies with a premium license could use. This outlines another advantage Storm-0558 had that should not have been available to them. Pay walling security feature that would cost £60 - £63 a month is a huge security flaw.
Damage & Implications

"The hack Storm-0558 conducted was not destructive, but they extracted information, which means the infrastructure was destroyed or attacked, just bypassed. The Attack happened over one month; there is no official number on how many businesses or governments were hacked."
Some of the high-level US diplomats targeted in the attack are as follows:
o Gina Raimondo (U.S. Secretary of Commerce)
o Nicholas Burns (U.S. Ambassador to China)
o Daniel Kritenbrink (Assistant Secretary of State for East Asian and Pacific Affairs)
o Congressman Don Bacon (U.S. Representative, R-Neb.)
There are two email systems used by the US diplomats, classified and unclassified. The Emails taken from the previously mentioned US diplomats were from the unclassified email system. This implies the emails taken were not top-secret material.
The implications of this attack are far outreached from the implications of a standard attack. This attack was not corporately backed, but state backed espionage group. This enters the realm of geopolitics.
The attack was completed at a critical time in US-Chinese diplomatic tensions. It happened in June 2023 when U.S. Secretary of State Antony Blinken was making a highly sensitive trip to Beijing, the first in five years, and the first since the spy balloon incident, where China sent spy balloons over the US.
By reading emails sent and received by the Commerce Secretary and the U.S. Ambassador to China, China most likely got the upper hand during negotiations by reading the negotiation strategies the US was going to implement during the discussion.
As a part of the outcome from the attack, the CSRB (U.S. Cyber Security Review Board) made a 34-page report released in April 2024 outlining how the attack was preventable and attributed it to a “cascade of security failures”. This report, being as damning as it was, left a scar on Microsoft.
The US government at the time of this attack only used one company, Microsoft, for its cloud infrastructure. This raised concerns about the US government having a “monoculture”, meaning they should outsource to more than one company, as it creates a single point of failure and the need for diversification to other companies, such as Google and Amazon AWS.
After the incident with paywalling features, Microsoft’s paradigm shifted. Microsoft now offer the SFI (Secure Future Initiative) that ensures that security is prioritised over releasing new features.
Mitigations & Defences
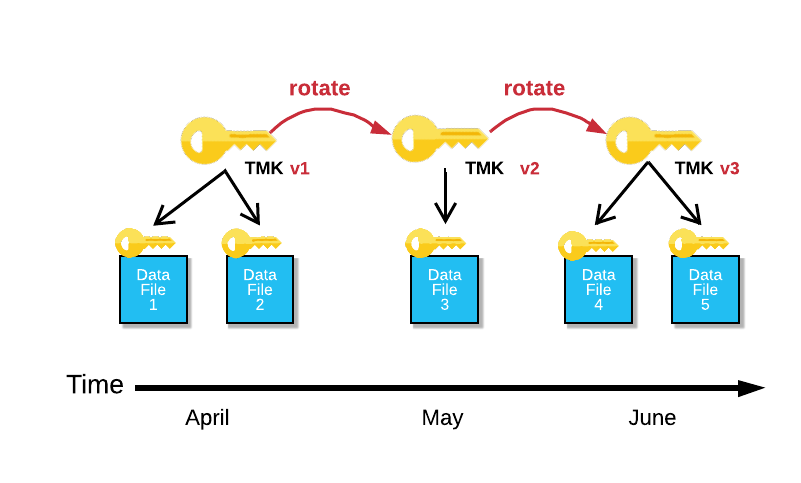
After identifying the attack, they acted swiftly by rotating the keys and making the 2016 MSA key so that it does not work with the enterprise environment. Rotating keys involves taking all active keys and methodically replacing them with new keys. This invalidates the old keys but keeps the system working for the new keys that take over. This means any old tokens generated by Storm-0558 will now not work, and any tokens made using the stolen key will also not work. The keys that are rotated are now done at a high frequency compared to the previous rotation of 5-7 years, as reported.
Another issue that Microsoft had to resolve was the paywall; this included Microsoft removing the “MailItemsAccessed” log from the E5 paywall and made them free to access for all “Microsoft Purview Audit (Standard)” members. This log allows systems to log what emails are accessed, not only who logs in, giving more in-depth analysis to system admins. Microsoft also took this a step further and made the log for this item last for 180 days instead of the 90 days it was previously. This boost of long-term log data also boosted the response, as it allows for more historical data to compare long attacks against in the future. The pressure to drop the paywall came from both CISA (Cybersecurity and Infrastructure Security Agency) and other companies that use Microsoft infrastructure.
The signing key system was not secure. To fix this, it has now been moved to an Azure confidential virtual machine. This machine is specifically made to encrypt the keys, not just when it is in rest/being stored, but when the key is in memory. This action prevents the memory leak issue that enabled the memory dump.
This was done after the CSRB report that introduced the secure by design program; more than 34,00 0 full-time engineers were hired to focus just on security implementation and architecture, making it the largest cybersecurity engineering project in history.
Conclusion
The storm-0558 Microsoft attack was both simple and well thought out. This article looked at the zombie key that was used and explained the systems it was used on, such as the authentication system used for generating and signing tokens. This whole attack stemmed from a single intrusion and spiderwebbed its way to other parts of Microsoft services.
This attack had a large geopolitical impact across the industry, both internationally, with the US diplomat's email being hacked, and technically, from the debate of being less reliant on one company for cloud services and security.
This attack ultimately forced both Microsoft and the tech industry to change paradigm and to focus on having no paywalls for critical security features and to have a secure-by-design architecture.
References
- https://www.microsoft.com/en-us/security/blog/2025/04/21/securing-our-future-april-2025-progress-report-on-microsofts-secure-future-initiative/
- https://www.cisa.gov/resources-tools/resources/CSRB-Review-Summer-2023-MEO-Intrusion
- https://www.cisa.gov/news-events/cybersecurity-advisories/aa23-193a
- https://www.microsoft.com/en-us/security/blog/2023/07/14/analysis-of-storm-0558-techniques-for-unauthorized-email-access/
- https://www.microsoft.com/en-us/security/blog/2023/11/02/announcing-microsoft-secure-future-initiative-to-advance-security-engineering/
- https://www.wiz.io/blog/key-takeaways-from-microsofts-latest-storm-0558-report
- https://www.cybersecuritydive.com/news/microsoft-free-security-logs-Outlook-email-hack-backlash/688388/
